
| Home | About | Plugins | Download | Screenshot | Support & Development |
Neural Network Nmap scanning optimization for non Windows based nodesPlugin Code: OSdetect_non_winDescription:
Analysis of the composition of the information collected during OS identification process, to identify key elements and their relations. This is where the statistical field and artificial neural network will be implemented and it has been successfully integrated in Core Impact which is distributed commercially. The plugin utilizes the first version of nmap-os-fingerprint (-o1). 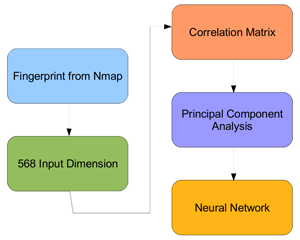 Plugin Simple Diagram You may download my presentation slides from here.
Neural Network Nmap scanning optimization for Windows based nodesPlugin Code: OSdetect_winDescription:
The classical method of OS fingerprinting is only involving the use of TCP/IP stack fingerprinting and still been used until now, for instance, Nmap which is based on classical fingerprinting.
There is another approach for OS fingerprinting which is focusing on the manipulation of information gained from port 135, MSRPC Endpoint Mapper. The technique will use the combination of UUID, annotation, protocol used and the endpoint discover from RPC endpoint mapper and later will be mapped on neural network by using perceptron network for the statistical on determine the result. This will ensure the accurate information regarding Windows version since the result will let the person know about its RPC architecture, informing on numbers of services and programs are available at the endpoint mapper. OSVDB Vulnerability ScannerPlugin Code: vuln_scanDescription:
With the correlation amongst the product_id, version_id and vendor_id, this correlation_id is then used to obtain the respective vulnerability. The issue thus far is that the correlation is made upon a larger subset when Nmap isn't able to populate the osmatch field. I have added checks on the generated osmatch but nonetheless, the accuracy depends on the OS identification
|